When it comes to endpoint security, knowing what policies you intended to deploy isn’t always the same as knowing what’s actually applied on a device. Between Intune, Group Policy, SCCM, and local configurations, security settings can quickly become difficult to validate—especially in complex or transitioning environments.
That’s where the Effective Settings page in Microsoft Defender for Endpoint comes in.
What Is the Effective Settings Page?
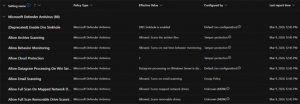
The Effective Settings page in Microsoft Defender for Endpoint (MDE) provides visibility into the actual Antivirus (AV), Attack Surface Reduction (ASR) rule, and other key security settings applied to a specific device. Rather than showing policy intent, this view reflects what is truly in effect on the endpoint itself. For our on-premises sysadmins, think “resultant set of policy” (RSOP), but in the cloud and specific to security configurations on a managed device.
For each AV or ASR rule, the page displays:
- Effective Value – the setting that is currently enforced on the device
- Configured By – the tool or source responsible for that setting, or said differently the tool or source that “won” the battle for precedence, such as:
- Intune
- Group Policy
- Tamper Protection
- Local Admin
- Default
- Unknown (conflicts)
This clarity is especially valuable when multiple management tools are in play or when policies don’t behave as expected.
Where to Find Effective Settings in Defender for Endpoint
You can access the Effective Settings page directly from the Defender portal by following this path:
Security Center → Assets → Devices → select a device → Configuration Management → Effective Settings
From the individual device view, security teams can quickly confirm how key endpoint protections are configured—without leaving the portal or logging into the device itself.
Note: The Effective Settings page currently supports Antivirus and ASR rule settings for Windows devices only.
Why Effective Settings Matter
The Effective Settings page significantly simplifies policy troubleshooting and validation.
Traditionally, confirming endpoint configurations required:
- Logging into devices directly
- Running PowerShell scripts
- Manually correlating policies across multiple management platforms
With Effective Settings, that work is consolidated into a single, authoritative view within Defender for Endpoint.
Real‑World Value for Security and IT Teams
The Effective Settings page is particularly useful in several common scenarios:
Faster Policy Troubleshooting
Whether AV or ASR policies are deployed through Intune, Group Policy, or SCCM, teams can quickly verify how those settings are applied on individual devices—making it easier to identify misconfigurations or conflicts.
Visibility Across Multiple Management Tools
Many organizations manage endpoints using more than one platform, either by design or during a migration. Effective Settings helps teams understand which tool ultimately won when policies overlap or conflict.
Support During Platform Migrations
For organizations transitioning from legacy management tools to modern management (such as moving from GPO or SCCM to Intune), this page provides a practical way to confirm that new policies are being enforced as intended—without disrupting users or devices.
A Practical Step Toward Operationalizing Defender for Endpoint
The Effective Settings page doesn’t introduce new security controls—but it does something just as important: it removes uncertainty. By showing exactly how AV and ASR rules are applied at the device level, Defender for Endpoint gives security teams the confidence to troubleshoot faster, reduce guesswork, and maintain consistent protection across their environment.
For organizations focused on operationalizing Microsoft security—not just deploying it—the Effective Settings page is a small feature that delivers meaningful day‑to‑day value.