Cyber threats are evolving faster than ever — and the ability to respond quickly, consistently, and at scale has become a core requirement for modern security operations.
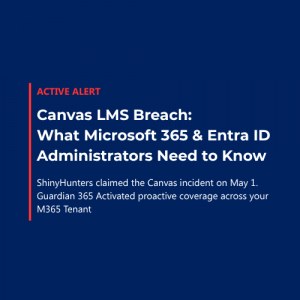
As part of ongoing enhancements to Guardian 365, Forsyte is introducing the Guardian 365 IOC Feed, a new capability powered by Inforcer that enables rapid deployment of defensive security controls across customer environments. To support this enhancement, all existing Guardian 365 customers are asked to complete (or re‑complete) Inforcer onboarding and formally confirm their participation in the IOC Feed by April 1, 2026.
Why This Matters Now
Recent geopolitical developments — including ongoing conflict in the Middle East — have coincided with increased cyber activity from both state‑aligned and opportunistic threat actors. These events reinforce a critical reality: threat actors move faster than traditional change control processes.
Guardian 365 is designed to help organizations stay ahead of these threats. Inforcer enables Forsyte’s SOC to deploy defensive security configurations at speed, including:
- Proactively blocking confirmed Indicators of Compromise (IOCs)
- Staging additional security configurations for customer review when credible intelligence indicates elevated risk
The new IOC Feed builds on this capability by improving the speed, consistency, and scale at which protections can be deployed across Guardian 365 customer environments.
What Is the Guardian 365 IOC Feed?
The Guardian 365 IOC Feed allows Forsyte’s SOC to deploy blocking rules for confirmed malicious infrastructure, including:
- Malicious IP addresses
- Domains
- Email sender addresses
- File hashes
These IOCs are sourced from government agencies, trusted cybersecurity vendors (including Microsoft), and Guardian 365 telemetry, and are only deployed once malicious activity has been validated.
How It Works
- IOC blocking rules are deployed immediately to provide instant protection
- Rules are applied across the Microsoft Defender XDR stack
- Customers receive an IOC bulletin prior to each deployment, including threat context and a full list of blocked indicators
Because emerging threats are unpredictable, IOC deployments do not follow a fixed schedule. Instead, Forsyte publishes IOC bulletins as needed, based on real‑time intelligence and observed threat activity.
Opt‑In vs. Opt‑Out: What’s the Difference?
Customers Who Opt In
By opting in, customers authorize Forsyte to:
- Deploy IOC blocking rules automatically through Inforcer
- Respond rapidly to emerging threats on the customer’s behalf
- Apply consistent protection across the Guardian 365 customer community
This enables Forsyte’s SOC to act immediately when high‑confidence threats are identified.
Customers Who Opt Out
Customers who opt out will:
- Continue receiving Guardian 365 threat communications and IOC details
- Assume responsibility for deploying defensive protections internally
In this case, IOC information is provided, but implementation rests with the customer’s IT or security team.
What Is Inforcer and Why It Matters
Inforcer is a cloud platform used by Guardian 365 to manage and deploy Microsoft 365 security configurations across customer environments.
Key capabilities include:
- Centralized security configuration management
- Automated policy deployment
- Faster rollout of security protections
- Continuous monitoring for configuration drift on critical controls (such as Conditional Access and Defender for Office 365 – in progress)
By leveraging Inforcer, Forsyte can deploy security improvements more efficiently and consistently, helping customers maintain a strong security posture without introducing unnecessary operational burden.
Value of Inforcer for Existing Guardian 365 Customers
Inforcer enhances Guardian 365 by enabling the SOC to rapidly deploy protections informed by real‑world threat intelligence and operational experience, including:
- Proactive IOC blocking
- Rapid deployment of Exchange transport rules for phishing campaigns
- Custom detection rules across Defender XDR
- Faster rollout of security posture improvements
Inforcer also supports continuous assessment of configuration health, helping detect and notify customers of drift in high‑impact security controls.
Security‑First Deployment Approach
Security controls deployed through Inforcer follow a risk‑based deployment model:
Deployed Actively
- IOC blocking rules are deployed in a live production state
- Used only for high‑urgency, validated threats
- Provide immediate protection against known malicious activity
Staged for Approval
- Policy changes, configuration updates, and structural improvements
- Deployed in report‑only, disabled, or unassigned states
- Activated only after customer review and approval
This ensures no end‑user‑impacting changes are deployed without authorization, while still enabling rapid defense against confirmed threats.
Inforcer Onboarding: What Customers Need to Do
To support the IOC Feed and ongoing Guardian 365 enhancements, customers must complete Inforcer onboarding by April 1, 2026.
High‑Level Steps
- Accept the Microsoft Partner Center (Indirect Reseller) relationship
- Accept the GDAP delegated access request
- Confirm successful integration provisioning
These approvals are part of Microsoft’s standard partner integration model and do not authorize Forsyte to sell licensing or make purchasing changes.
Your Customer Success Account Manager (CSAM) will guide you through the process and provide the required approval links.
Key Takeaway for IT & Security Leaders
The Guardian 365 IOC Feed and Inforcer onboarding are designed to help organizations:
- Respond faster to emerging threats
- Reduce operational friction during high‑risk events
- Maintain consistent protection across Microsoft 365 environments
Completing onboarding and confirming IOC Feed participation ensures your organization can take full advantage of these capabilities — without sacrificing visibility or control.
Action Required
Complete Inforcer onboarding and confirm IOC Feed participation by April 1, 2026.
Contact your Guardian 365 CSAM to get started or ask questions.