Understanding Azure Active Active
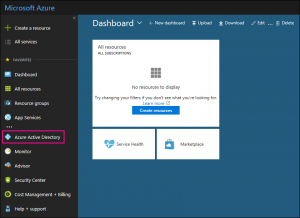
Azure Active Directory, commonly referred to as Azure AD, is a Microsoft subscription available for free with paid subscriptions to Microsoft 365, Microsoft Dynamics DRM Online, Enterprise Mobility Suite, or other Microsoft services. Admins can create and manage user and group accounts by signing into an account in the Azure portal (image below).
Azure AD Helps Users Sign Into and Access Resources
- External resources, such as Microsoft 365, the Azure portal, and thousands of other SaaS applications.
- Internal resources, such as apps on a corporate network and intranet, along with cloud apps developed by your own organization.
Azure AD is intended for:
IT admins. Use Azure AD to control access to your apps and your app resources, based on your business requirements. For example, you can use Azure AD to require multi-factor authentication when accessing important organizational resources. Additionally, you can use Azure AD to automate user provisioning between your existing Windows Server AD and your cloud apps, including Microsoft 365. Finally, Azure AD gives you powerful tools to automatically help protect user identities and credentials and to meet your access governance requirements. To get started, sign up for a free 30-day Azure Active Directory Premium trial.
App developers. Use Azure AD as a standards-based approach for adding single sign-on (SSO) to your app, allowing it to work with a user’s pre-existing credentials. Azure AD also provides APIs that can help you build personalized app experiences using existing organizational data. To get started, sign up for a free 30-day Azure Active Directory Premium trial. For more information, you can also see Azure Active Directory for developers.
Microsoft 365, Office 365, Azure, or Dynamics CRM Online subscribers. Each Microsoft 365, Office 365, Azure, and Dynamics CRM Online tenant is automatically an Azure AD tenant. You can immediately start to manage access to your integrated cloud apps.
Microsoft 365 Identity Models and Azure AD
Getting your identity infrastructure configured correctly is vital to managing Microsoft 365 user access and permissions for your organization. There are two identity models in Microsoft 365: you can maintain your organization’s identities only in the cloud, or you can maintain your on-premises Active Directory Domain Services (AD DS) identities and use them for authentication when users access Microsoft 365 cloud services.
| Attribute | Cloud-only Identity | Hybrid Identity |
|---|---|---|
| Definition | User account only exists in the Azure AD tenant for your Microsoft 365 subscription. | User account exists in AD DS and a copy is also in the Azure AD tenant for your Microsoft 365 subscription. The user account in Azure AD might also include a hashed version of the already hashed AD DS user account password. |
| How Microsoft 365 authenticates user credentials | The Azure AD tenant for your Microsoft 365 subscription performs the authentication with the cloud identity account. | The Azure AD tenant for your Microsoft 365 subscription either handles the authentication process or redirects the user to another identity provider. |
| Best for | Organizations that do not have or need an on-premises AD DS. | Organizations using AD DS or another identity provider. |
| Greatest benefit | Simple to use. No extra directory tools or servers required. | Users can use the same credentials when accessing on-premises or cloud-based resources. |
Azure AD Licenses
- Azure Active Directory Free. Provides user and group management, on-premises directory synchronization, basic reports, self-service password change for cloud users, and single sign-on across Azure, Microsoft 365, and many popular SaaS apps.
- Azure Active Directory Premium P1. In addition to the Free features, P1 also lets your hybrid users access both on-premises and cloud resources. It also supports advanced administration, such as dynamic groups, self-service group management, Microsoft Identity Manager (an on-premises identity and access management suite) and cloud write-back capabilities, which allow self-service password reset for your on-premises users.
- Azure Active Directory Premium P2. In addition to the Free and P1 features, P2 also offers Azure Active Directory Identity Protection to help provide risk-based Conditional Access to your apps and critical company data and Privileged Identity Management to help discover, restrict, and monitor administrators and their access to resources and to provide just-in-time access when needed.
- “Pay as you go” feature licenses. You can also get additional feature licenses, such as Azure Active Directory Business-to-Customer (B2C). B2C can help you provide identity and access management solutions for your customer-facing apps. For more information, see Azure Active Directory B2C documentation.
Azure AD Features
| Category | Description |
|---|---|
| Application management | Manage your cloud and on-premises apps using Application Proxy, single sign-on, the My Apps portal (also known as the Access panel), and Software as a Service (SaaS) apps. For more information, see How to provide secure remote access to on-premises applications and Application Management documentation. |
| Authentication | Manage Azure Active Directory self-service password reset, Multi-Factor Authentication, custom banned password list, and smart lockout. For more information, see Azure AD Authentication documentation. |
| Azure Active Directory for developers | Build apps that sign in all Microsoft identities, get tokens to call Microsoft Graph, other Microsoft APIs, or custom APIs. For more information, see Microsoft identity platform (Azure Active Directory for developers). |
| Business-to-Business (B2B) | Manage your guest users and external partners, while maintaining control over your own corporate data. For more information, see Azure Active Directory B2B documentation. |
| Business-to-Customer (B2C) | Customize and control how users sign up, sign in, and manage their profiles when using your apps. For more information, see Azure Active Directory B2C documentation. |
| Conditional Access | Manage access to your cloud apps. For more information, see Azure AD Conditional Access documentation. |
| Device Management | Manage how your cloud or on-premises devices access your corporate data. For more information, see Azure AD Device Management documentation. |
| Domain Services | Join Azure virtual machines to a domain without using domain controllers. For more information, see Azure AD Domain Services documentation. |
| Enterprise Users | Manage license assignment, access to apps, and set up delegates using groups and administrator roles. For more information, see Azure Active Directory user management documentation. |
| Hybrid Identity | Use Azure Active Directory Connect and Connect Health to provide a single user identity for authentication and authorization to all resources, regardless of location (cloud or on-premises). For more information, see Hybrid identity documentation. |
| Identity Governance | Manage your organization’s identity through employee, business partner, vendor, service, and app access controls. You can also perform access reviews. For more information, see Azure AD identity governance documentation and Azure AD access reviews. |
| Identity Protection | Detect potential vulnerabilities affecting your organization’s identities, configure policies to respond to suspicious actions, and then take appropriate action to resolve them. For more information, see Azure AD Identity Protection. |
| Managed Identities for Azure Resources | Provides your Azure services with an automatically managed identity in Azure AD that can authenticate any Azure AD-supported authentication service, including Key Vault. For more information, see What is managed identities for Azure resources?. |
| Privileged Identity Management (PIM) | Manage, control, and monitor access within your organization. This feature includes access to resources in Azure AD and Azure, and other Microsoft Online Services, like Microsoft 365 or Intune. For more information, see Azure AD Privileged Identity Management. |
| Reports and Monitoring | Gain insights into the security and usage patterns in your environment. For more information, see Azure Active Directory reports and monitoring. |
Microsoft Terms for Understanding Azure AD
| Term or Concept | Description |
|---|---|
| Identity | A thing that can get authenticated. An identity can be a user with a username and password. Identities also include applications or other servers that might require authentication through secret keys or certificates. |
| Account | An identity that has data associated with it. You cannot have an account without an identity. |
| Azure AD Account | An identity created through Azure AD or another Microsoft cloud service, such as Microsoft 365. Identities are stored in Azure AD and accessible to your organization’s cloud service subscriptions. This account is also sometimes called a Work or school account. |
| Account Administrator | This classic subscription administrator role is conceptually the billing owner of a subscription. This role enables you to manage all subscriptions in an account. For more information, see Classic subscription administrator roles, Azure roles, and Azure AD administrator roles. |
| Service Administrator | This classic subscription administrator role enables you to manage all Azure resources, including access. This role has the equivalent access of a user who is assigned the Owner role at the subscription scope. For more information, see Classic subscription administrator roles, Azure roles, and Azure AD administrator roles. |
| Owner | This role helps you manage all Azure resources, including access. This role is built on a newer authorization system called Azure role-based access control (Azure RBAC) that provides fine-grained access management to Azure resources. For more information, see Classic subscription administrator roles, Azure roles, and Azure AD administrator roles. |
| Azure AD Global Administrator | This administrator role is automatically assigned to whomever created the Azure AD tenant. Global administrators can do all of the administrative functions for Azure AD and any services that federate to Azure AD, such as Exchange Online, SharePoint Online, and Skype for Business Online. You can have multiple Global administrators, but only Global administrators can assign administrator roles (including assigning other Global administrators) to users. For more information about the various administrator roles, see Administrator role permissions in Azure Active Directory. |
| Azure Subscription | Used to pay for Azure cloud services. You can have many subscriptions and they’re linked to a credit card. |
| Azure Tenant | A dedicated and trusted instance of Azure AD that’s automatically created when your organization signs up for a Microsoft cloud service subscription, such as Microsoft Azure, Microsoft Intune, or Microsoft 365. An Azure tenant represents a single organization. |
| Single Tenant | Azure tenants that access other services in a dedicated environment are considered single tenant. |
| Multi-tenant | Azure tenants that access other services in a shared environment, across multiple organizations, are considered multi-tenant. |
| Azure AD Directory | Each Azure tenant has a dedicated and trusted Azure AD directory. The Azure AD directory includes the tenant’s users, groups, and apps and is used to perform identity and access management functions for tenant resources. |
| Custom Domain | Every new Azure AD directory comes with an initial domain name, domainname.onmicrosoft.com. In addition to that initial name, you can also add your organization’s domain names, which include the names you use to do business and your users use to access your organization’s resources, to the list. Adding custom domain names helps you to create user names that are familiar to your users, such as alain@contoso.com. |
| Microsoft Account (also called, MSA) | Personal accounts that provide access to your consumer-oriented Microsoft products and cloud services, such as Outlook, OneDrive, Xbox LIVE, or Microsoft 365. Your Microsoft account is created and stored in the Microsoft consumer identity account system that’s run by Microsoft. |
Understanding the value of Azure AD
Understanding the value of Azure AD has become the backbone of many organization’s security and management of user identities behind the scenes. At Forsyte, we help organizations plan and prepare for what’s next. We champion workload integrations and subscription assessments so our clients understand what is available in various Microsoft 365 licenses and how to make the most of them.
Oftentimes, this increases the value of the owned Microsoft 365 solutions by eliminating disparate platforms and apps.
Contact sales@forsyteit.com to discuss Azure AD subscriptions, migration, management, and a roadmap for success!